El març de 1989, l’enginyer britànic Tim Berners‑Lee va presentar al CERN el protocol que esdevindria la World Wide Web. En lloc de patentar‑la, la va alliberar perquè tothom pogués compartir coneixement sense fronteres. Aquell gest va encendre la flama d’un Internet obert, descentralitzat i profundament humà que va impulsar avenços científics, culturals i econòmics sense precedents
Cybersecurity in 2024: Key Incidents and Emerging Trends in a Complex Threat Landscape
In 2024, the cybersecurity landscape has been marked by a significant escalation in both the frequency and sophistication of cyberattacks. Notable incidents have disrupted major corporations and critical infrastructure, underscoring the urgent need for robust cybersecurity measures. This article examines the current state of cybersecurity, highlighting key incidents and trends that have defined the year.
The Use of Pagers in Cyberattacks: A Lurking Threat?
In a world where digital devices proliferate, the security community must consider the possibility of outdated technologies, such as pagers, being repurposed for malicious intent. While most discussions center around modern cyber threats, pagers—though considered obsolete—could be exploited as a deadly weapon delivery mechanism. This article explores the vulnerabilities and risks posed by this underexplored attack vector.
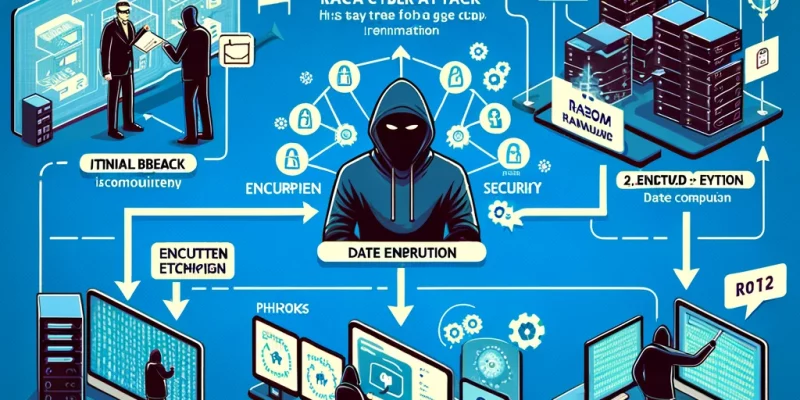
The Ransomware Crisis in Mid-2024: An Escalating Threat Landscape
Ransomware attacks continue to escalate in 2024, with cybercriminals adopting increasingly sophisticated techniques that challenge traditional cybersecurity measures. The rise of AI-powered ransomware, the targeting of critical infrastructure, and the emergence of double and triple extortion tactics have created a volatile landscape that demands urgent attention. This article delves into the current ransomware situation, exploring the key trends, notable incidents, and evolving strategies that both attackers and defenders are employing in the ongoing battle for cyber supremacy.
The July DDoS Attack on Microsoft: Analyzing the Economic and Security Impact
In July 2024, Microsoft faced one of the most significant Distributed Denial-of-Service (DDoS) attacks in its history, affecting multiple services and causing widespread disruption. This DDoS assault, peaking at over 3 terabits per second (Tbps), targeted key services including Azure, Microsoft 365, and Xbox Live, impacting millions of users globally. The attack underscored the escalating scale and sophistication of cyber threats, highlighting vulnerabilities even in the infrastructures of tech giants.
The Possibility of a Total Internet Blackout: Causes and Consequences
Understanding the multifaceted threat of a total internet blackout is essential for taking proactive measures to safeguard critical infrastructure and ensure the continued functionality of the global internet. As we approach a period of increased solar activity, vigilance and preparedness are crucial to mitigating potential disruptions.
Microsoft Outage: Analyzing the Disruption and Its Causes
On July 19, 2024, a significant outage disrupted Microsoft services, affecting millions of users worldwide. This article delves into the various speculations and official statements surrounding the incident, providing a comprehensive analysis of the possible causes and the broader implications for cybersecurity.
How to Keep Your Art Out of AI Generators and the Potential for Hacking AI Systems
As AI technologies advance, the risk of unauthorized use of digital art by AI generators has become a significant concern for artists. This article explores practical steps artists can take to protect their work from AI scraping and delves into how these strategies might be exploited to hack AI learning systems. By understanding the mechanics of AI training and employing robust protective measures, artists can safeguard their creations while contributing to the broader discourse on ethical AI development.
Global Operation Takes Down 600 Cybercrime Servers Linked to Cobalt Strike
In a landmark international effort, law enforcement agencies have dismantled nearly 600 servers linked to cybercriminal activities involving Cobalt Strike, a tool often misused for malicious purposes. This operation, codenamed MORPHEUS, spanned 27 countries and targeted unauthorized versions of the software. The crackdown aims to curb the proliferation of ransomware and other cyber threats enabled by Cobalt Strike’s misuse, highlighting the ongoing global struggle against sophisticated cybercrime networks.
The 2024 Ransomware Attack on England’s Health System: Life-Threatening Impact of Cybercrime
In the early hours of May 14, 2024, England’s National Health Service (NHS) experienced an unprecedented ransomware attack, crippling hospitals and endangering countless lives. This incident has highlighted the severe, life-threatening implications of cybercrime on critical infrastructure, underscoring the urgent need for enhanced cybersecurity measures within healthcare systems.
The Recent Hack on Spain’s DGT: An In-Depth Analysis
In a significant cybersecurity breach, Spain’s Directorate-General for Traffic (DGT) fell victim to a sophisticated cyberattack, compromising sensitive data and disrupting essential services. This article delves into the details of the attack, examining the methods used, the impact on the DGT, and the broader implications for national cybersecurity.
Cracking Randomly Generated Numbers in Computer Systems: Methods and Implications
Random number generation (RNG) is a cornerstone of modern computing, critical for cryptographic security, simulations, gaming, and more. However, the quest for true randomness in RNGs presents a significant challenge. This article explores the techniques used to crack RNGs, the implications of these vulnerabilities, and the measures necessary to fortify RNG security.
Shielding Small Businesses from Ransomware: A Strategic Guide
Ransomware poses a significant threat to small businesses due to their often limited cybersecurity resources. This article provides a comprehensive strategy for small business owners to protect their digital assets from ransomware attacks, including preventive measures, employee training, and response planning.
The Rise of Technofeudalism: Exploring Digital Dominance in the 21st Century
Technofeudalism is a concept that has gained traction in recent years, especially as digital technologies increasingly shape economic and social structures globally. This term is used to describe a new socioeconomic system where control over technology—and by extension, over economic and societal norms—is concentrated in the hands of a few tech giants. This article explores the origins, implications, and critical responses to the concept of technofeudalism.
Navigating the Digital Storm: The Iddink Cyber Incident of 2024
The Iddink Group, a major provider of educational materials, experienced a significant cyber incident. This attack, part of a broader trend of increasing cyber threats targeting educational and other critical sectors, underscores the evolving complexity and impact of cybersecurity breaches on global infrastructure.
Analyzing the Massive Health Insurance Data Breach in France
A significant data breach impacted over 33 million individuals in France, compromising sensitive information from health insurance companies. The breach reveals potential vulnerabilities in data protection practices and highlights the critical need for robust cybersecurity measures.
Hackers in Cinema: A Chronological Journey
In the realm of cinema, hackers have been portrayed as both heroes and villains, embodying the societal ambivalence towards technology and its power. The 1983 classic “WarGames” introduced audiences to the concept of hacking through a high school student who accidentally hacks into a military supercomputer, illustrating the potential global consequences of cyber interference. This film not only entertained but also sparked a serious dialogue about the need for cybersecurity measures.
The Future of Digital Identity: Navigating the Cybersecurity Landscape
The Future of Digital Identity: Navigating the Cybersecurity Landscape In the digital age, identity is a cornerstone of every interaction, transaction, and online activity. The evolution of digital identity systems towards more integrated and universally accepted forms is seen as a pivotal step in securing and streamlining digital services. However, this evolution comes with significant […]
Navigating the Landscape of Fraudulent GPT Applications: Challenges and Solutions
The rapid advancement in Generative Pre-trained Transformers (GPT) technology has ushered in a new era of innovation across various sectors. However, this progress is not without its dark side, as fraudulent GPT applications have emerged as a significant threat. This article delves into the mechanisms of these fraudulent activities, their implications for individuals and businesses, and the multifaceted strategies required to combat them effectively. It underscores the importance of a collaborative approach involving technology, law, and awareness to safeguard against the misuse of GPT technology.
Cybersecurity Essentials for Families: Protecting Your Digital Home
Cybersecurity for families is about more than just protecting devices; it’s about safeguarding your family’s digital lifestyle. By understanding key concepts and implementing strategic protections, you can create a secure digital environment that shields your loved ones from cyber threats. Stay informed, stay secure, and navigate the digital world with confidence.
The Free Software Movement: A Comprehensive Exploration
This article provides an in-depth analysis of the free software movement, exploring its origins, principles, and impact. Highlighting the significant contributions of Richard Stallman and the Free Software Foundation, it delves into the philosophical underpinnings and ongoing relevance of this movement in the digital age.
A Comprehensive Analysis of the Orange Cyber Attack Incident
This article delves into the cyber attack that significantly disrupted the operations of Orange, a major telecommunications operator in Spain. The incident, which primarily involved unauthorized access to the company’s RIPE (Réseaux IP Européens Network Coordination Centre) account, resulted in widespread internet service outages across the country. The following analysis examines the nature of the attack, its execution, and the broader implications for cybersecurity in the telecommunications sector.
Unraveling Ecsypno: Embracing Self-Conducted Cybersecurity Testing for Enhanced Protection
Ecsypno stands as a beacon in cybersecurity, offering self-testing capabilities critical in the modern digital landscape. It empowers organizations to proactively identify and address vulnerabilities, ensuring a robust defense against evolving cyber threats. This tool redefines the approach to digital security, making in-house testing not only viable but essential.
Digital Transformation in Developing Countries: Bridging the Technological Divide
Digital transformation in developing countries is a crucial step towards economic, social, and technological advancement. This article delves into the unique challenges and opportunities these nations face in the digital era. We explore case studies, strategies for successful integration, and the potential impacts on various sectors.
Cyber Incidents in the Last Hours of December 31: A Comprehensive Analysis
As the world gears up to celebrate the new year, the final hours of December 31st become a critical period for cybersecurity. This time is marked by a notable increase in cyber activities, providing a ripe scenario for cyber attackers to exploit vulnerabilities. From Distributed Denial of Service (DDoS) attacks disrupting online services to intricate phishing campaigns targeting unsuspecting users, the range of cyber incidents during these hours is diverse and complex
The Pioneering Discovery of SQL Injection: A Look Back at December 25, 1998
The discovery of SQL Injection on December 25, 1998, marked a critical milestone in the field of cybersecurity. This technique, which manipulates SQL queries by injecting malicious code, exposed profound vulnerabilities in database management of web applications. It underscored the necessity of stringent input validation and advanced security protocols in software development, fostering a new era of cybersecurity awareness and preventive measures against such sophisticated attacks
The Legality of Owning a Computer with Kali Linux: Navigating Freedom and Responsibility
In the cybersecurity realm, Kali Linux stands as a legal, open-source operating system used for ethical hacking and penetration testing. While owning a computer with Kali Linux is lawful, its use becomes illegal if employed for unauthorized hacking, known as black-hat hacking. Users must obtain proper authorization for ethical hacking, distinguishing legal practices from illicit activities. Misconceptions about Kali Linux persist, underscoring the need for public awareness about its legitimate and professional applications.
Digital Deception: Unmasking Email Hacking Techniques Used in Identity Supplantation
In the realm of email hacking for identity supplantation, phishing stands out as a primary technique. Cybercriminals craft emails that appear legitimate, skillfully mimicking the language and style of trusted sources. These deceptive messages often contain links or attachments that, when accessed, compromise the recipient’s personal information or credentials. Understanding and identifying these phishing attempts is crucial for protecting against identity theft and maintaining email security
Navigating the Privacy Paradox: The Risks and Realities of Central Bank Digital Currencies (CBDCs)
Central Bank Digital Currencies (CBDCs) represent a significant evolution in the landscape of monetary policy and digital finance. While they offer numerous advantages such as financial inclusion and improved efficiency in transactions, CBDCs also introduce complex challenges regarding individual privacy. This article delves into the nuanced implications of CBDCs for personal privacy, exploring potential risks and how they might reshape the relationship between individuals, financial institutions, and governments.
Embracing Open Source: The Critical Role of Linux in Public Administration and a Comprehensive Guide for Transitioning from Proprietary to Open Source Software
The adoption of Linux and open source software in public administration marks a significant shift in how government bodies manage their IT infrastructure. This movement towards open source solutions is driven by the need for cost-effectiveness, transparency, flexibility, and security. This article delves into the crucial role of Linux in public administration and provides a detailed guide on transitioning from proprietary to open-source software, ensuring a smooth and efficient transformation
Navigating the Abyss: Understanding and Preparing for Total Internet Shutdown Scenarios
This article offers a comprehensive exploration of the total internet shutdown theory, providing insights into its feasibility, causes, impacts, and the strategies required for mitigation and response. The accompanying image vividly portrays the stark reality of a world plunged into darkness by such a shutdown, underscoring the urgency of addressing this critical issue.
Embracing Digital Transformation in Dental Laboratories: A Comprehensive Overview
This article is a comprehensive exploration of the digital transformation in dental laboratories, covering historical context, key technologies, impacts on quality and efficiency, customization aspects, challenges, and future trends. It is designed for readers seeking an in-depth understanding of how digital innovation is revolutionizing this field.
Bracing for 2024: A Strategic Outlook on Cybersecurity Threats and Defenses
As we approach 2024, the cybersecurity landscape continues to be a battleground of evolving threats and sophisticated attacks. This article aims to provide a strategic overview of the anticipated cybersecurity threats in 2024. It also offers insights into effective defense mechanisms, underscoring the need for proactive measures in an increasingly digital world.
Navigating the Digital Age: A Parent’s Guide to Combating Cyberbullying
In the ever-evolving digital landscape, cyberbullying has emerged as a significant concern for parents. The anonymity and reach of the internet can embolden individuals to engage in harmful behaviors, impacting the mental and emotional well-being of children. This article aims to provide parents with comprehensive insights and practical strategies to combat cyberbullying, ensuring a safer online environment for their children.
Blockchain in Pharmaceuticals
Blockchain technology, initially associated with cryptocurrencies, has grown to become a transformative force in various industries, including pharmaceuticals. Its potential to revolutionize the pharmaceutical industry is significant, given the sector’s complex supply chains, stringent regulatory requirements, and the critical need for data integrity and security. This article explores how blockchain can be applied in pharmaceutical laboratories, enhancing efficiency, security, and compliance.
Navigating the Digital Frontier: Transformative Strategies for Retail Excellence
Digital transformation in the retail sector is a crucial strategy for businesses looking to thrive in an increasingly digital world. The integration of digital technology into all areas of business fundamentally changes how operations are conducted and value is delivered to customers. Retailers must adapt to these changes to remain competitive and meet the evolving […]
Understanding the Human Factor in Digital Transformation
Digital transformation in small companies is a critical process that involves not just the adoption of new technologies, but also a significant shift in culture and mindset. This transformation is particularly challenging because of the human factor and resistance to change that often accompanies it. In this article, we will explore these challenges and offer strategies for successfully implementing digital transformation in small businesses, with a focus on process improvements.
Ransomware Attacks on Schools and Universities: Counting the Economic and Social Costs
Introduction In recent years, ransomware attacks have emerged as a significant threat to educational institutions, including schools and universities. These attacks not only disrupt the normal functioning of these institutions but also expose confidential data, putting the security and privacy of students and staff at risk. In this article, we will delve into recent incidents […]
Small businesses to receive cyber security boost
Australia’s recent cybersecurity strategy for the period 2023-2030 marks a significant shift in the country’s approach to cyber defense. The strategy, under the leadership of the Minister for Cyber Security, Clare O’Neil, focuses on protecting not just the critical infrastructure but also extends its shield to cover small and medium businesses, which are often more […]
The Escalating Cost of Ransomware
In the last year, ransomware attacks have not only increased in frequency but also in sophistication, leading to unprecedented economic losses. According to a report by Cybersecurity Ventures, global ransomware damage costs were estimated to exceed $20 billion in 2022, a staggering increase from $11.5 billion in 2019. This exponential rise reflects the growing boldness […]
The Escalating Threat
This article offers an overview of the critical issue of ransomware attacks on healthcare systems. While specific numbers and case studies could vary, the general trends and recommendations remain relevant and imperative for addressing this growing threat.
Navigating the Digital Landscape: Cybersecurity Risks for the Third Age
This article aims to provide a comprehensive overview of the cybersecurity challenges faced by older adults, along with practical advice and future perspectives. The focus is on empowering this demographic to become more resilient against cyber threats while emphasizing the role of community and family in this endeavor.
Navigating Digital Waters: A Guide to Understanding and Preventing Phishing Attacks
In the ever-evolving digital world, cybersecurity threats have become increasingly sophisticated, with phishing being one of the most prevalent and perilous. Phishing is a cybercrime in which individuals are contacted by email, telephone, or text message by someone posing as a legitimate institution to lure individuals into providing sensitive data such as personally identifiable information, […]
Cyber Resilience: Fortifying Organizations in the Digital Age
In the ever-evolving landscape of digital technology, the concept of “cyber resilience” has emerged as a vital strategy for organizations striving to safeguard their digital assets and operations. This approach transcends traditional cybersecurity measures, integrating robust defense mechanisms with proactive planning to ensure an organization can withstand and quickly recover from cyber incidents. Understanding Cyber […]
Discover the Thrill of Digital Resistance in ‘Resistiu’: A Riveting Tale of Hacktivism and the Fight for Freedom
The crowdfunding campaign for “Resistiu,” by Òscar Bermell Massana, presents a gripping narrative that is both timely and thought-provoking. The story follows Cafard, a hacker who leads a cyberactivist cell aiming to topple Minister Zoscos, accused of repeatedly violating fundamental rights. This conflict blurs the lines between the hacker’s digital alter-ego and their real identity, […]
Digital Shields in Verse: Fortifying Cyber Realms Against Invisible Foes
In the ever-evolving digital landscape, cybersecurity has become a paramount concern for organizations and individuals alike. The surge in cyber threats and attacks necessitates robust strategies to minimize exposure and strengthen defenses. Among these strategies, the use of continuous vulnerability scanners emerges as a key tactic. 1. Continuous Vulnerability Scanners: A Proactive Approach 2. Regularly […]
Fortifying Digital Frontiers: The Imperative of Continuous Vulnerability Scanning and Periodic Cybersecurity Audits
In today’s digital age, where data breaches and cyber attacks are as frequent as they are damaging, the need for robust cybersecurity measures has never been more pressing. Among these, two stand out for their proactive approach in safeguarding digital assets: continuous vulnerability scanning and periodic cybersecurity audits. Continuous vulnerability scanning is akin to a […]
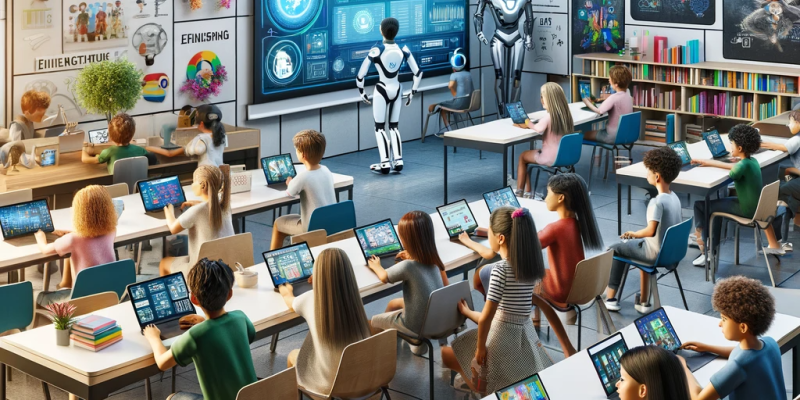
Digital Transformation in Education: Revolutionizing Learning from Elementary to University
Introduction The realm of education is undergoing a profound transformation, propelled by digital innovations. The way we teach and learn at different educational levels – elementary school, high school, and university – is evolving rapidly, embracing a future where digital tools and approaches redefine the educational landscape. Elementary School: Foundations in the Digital Age High […]
Cybersecurity in the Educational Landscape: Balancing Digital Innovation with Safety
Introduction: The integration of technology into the educational environment has transformed the way teaching and learning occur. While these advancements have unlocked new horizons of knowledge accessibility and pedagogical methods, they also present significant cybersecurity challenges. Educational institutions are now faced with the dual task of incorporating technology into their curriculum and ensuring the protection […]
Savoring the Digital Flavor: Midterm ROI in the Food Industry’s Tech Revolution
Introduction: The food industry, a cornerstone of the global economy, is undergoing a profound transformation. Digital technology is not just a garnish on the side; it’s becoming the main course of business strategies. This transformation goes beyond mere automation; it represents an integrative approach to managing supply chains, customer experiences, production lines, and marketing channels. […]
The Imperative of Implementing a Cyber-Incident Notification System for Mid-Size Companies
Introduction In today’s digital age, the importance of cybersecurity cannot be overstated. Cyberattacks have become increasingly sophisticated, targeting organizations of all sizes. Mid-size companies, in particular, have become prime targets due to their valuable data and often less robust security measures compared to large enterprises. To mitigate the risks and potential damage caused by cyber […]
The Crumbling Cookie: Consequences of a Cyberattack on Food Factories
Introduction: In an age where technology permeates every aspect of life, cyber threats have become a prominent concern, extending beyond digital confines to tangibly affect our daily bread – or in this case, our cookies. A cyberattack on a food factory, such as a cookie manufacturing plant, can have wide-ranging consequences that affect not only […]
The Crucial Role of Continuous Vulnerability Checks in Sustaining Business Continuity
In an age where the digital landscape is as volatile as it is indispensable, the importance of a robust continuous vulnerability check policy cannot be overstated. Businesses of all sizes face an array of cyber threats, from phishing scams to advanced persistent threats, which have the potential to disrupt operations and cause significant financial and […]
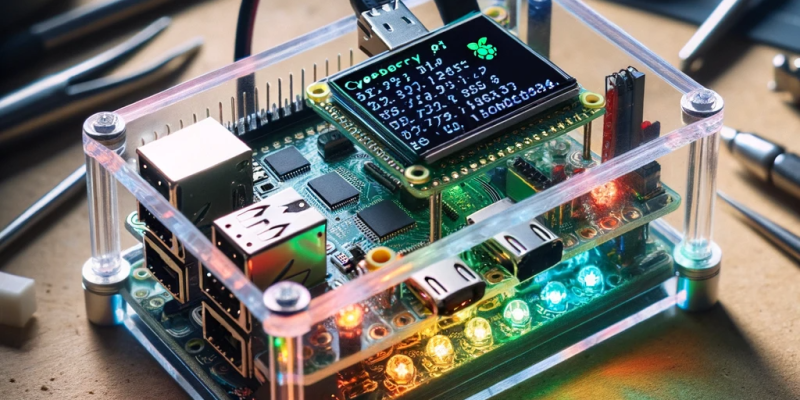
Harnessing the Power of EVA: Advancing Cybersecurity in Medium Enterprises
In the rapidly evolving digital landscape, cybersecurity is not just a necessity but a critical investment, particularly for medium-sized enterprises that often face unique challenges. They must balance resource allocation between growth and protection, often operating with less financial flexibility than larger corporations. This is where devices like EVA (Enterprise Vulnerability Analyzer) come into play, […]
Fortifying HPLC Systems in the Pharmaceutical Industry: A Cybersecurity Perspective
Introduction: High-Performance Liquid Chromatography (HPLC) is a cornerstone analytical technique in the pharmaceutical industry, crucial for ensuring the quality and purity of products. With the advent of sophisticated data systems and increased connectivity, HPLC systems, like many other aspects of pharmaceutical operations, have become part of a networked environment. This integration, while beneficial for efficiency […]
Navigating the Skies with Precision: Digital Transformation in Aviation Flight Planning
Introduction Flight planning is a critical component of the aviation industry, ensuring the safety and efficiency of air travel. Traditionally, flight planning has been a complex and time-consuming task, requiring pilots and dispatchers to analyze weather data, air traffic, and various operational factors manually. However, the aviation industry is now experiencing a significant shift – […]
Navigating the Skies of the Future: Digital Transformation in Aviation Maintenance
Introduction The aviation industry has always been at the forefront of technological innovation, pushing the boundaries of what is possible in human travel. From the Wright brothers’ first powered flight in 1903 to the advanced aircraft we have today, aviation has come a long way. But the evolution of aviation isn’t just about the planes […]
Unlocking the Future: Digital Transformation in the Pharmaceutical Industry
The pharmaceutical industry, traditionally known for its conservative and highly regulated nature, is undergoing a remarkable evolution. Digital transformation has emerged as a powerful force, reshaping the way pharmaceutical companies operate, from research and development to manufacturing, distribution, and patient care. This seismic shift is not just about embracing technology; it’s about rewriting the rules […]
Small Bussines World!
In today’s digital world, efficiency and simplicity are essential elements for success. As web technologies advance, two distinct approaches to meeting user needs are emerging: small, specialized web applications and centralized solutions that aim to do it all. In this article, we’ll explore why small web applications that perform a single function outperform centralized solutions […]
Cybersecurity in Physical Credit Card Payments
Introduction In an era dominated by digital transactions and online shopping, it’s easy to overlook the potential cybersecurity threats that still exist in physical credit card payments. While advancements in technology have improved security measures, the risks associated with using physical credit cards persist. This article explores the dangers of cybersecurity threats when paying with […]